The seven-year gap is the story, not the CVE
Microsoft patched CVE-2018-8639 in December 2018. CISA added it to the KEV catalog in March 2025. The interesting number isn't the bug's age — it's the distance between when a fix shipped and when the exposed fleet was acknowledged.
Microsoft shipped the fix for CVE-2018-8639 on December 11, 2018. CISA added it to the Known Exploited Vulnerabilities catalog on March 3, 2025, with a 21-day federal remediation deadline. Seven years and three months separate those two dates. The bug did not get worse in March 2025. The patch did not get less effective. What changed is harder to name, and that is the part worth paying attention to.
The obvious read
A Windows Win32k local privilege escalation, CWE-404, CVSS 7.8, marked “Exploitation Detected” at release. An authenticated low-privileged user runs crafted code; Win32k mishandles an object in memory; the user ends up executing in kernel mode. Microsoft’s December 2018 cumulative updates closed it across the entire then-supported lineup: Windows 7 SP1, Windows 8.1, Windows 10 versions 1507 through 1809, Windows Server 2008 SP2 and R2 SP1, Server 2012 and 2012 R2, Server 2016, Server 2019. The relevant KBs include KB4471318 and KB4471328 for Server 2008 R2 and Windows 7, KB4471321 for Windows 10 1607 and Server 2016, KB4471324 for Windows 10 1809 and Server 2019, and KB4471320 / KB4471322 for Windows 8.1 and Server 2012 R2. If a host received its December 2018 cumulative update, the host is fixed. End of story for that host.
Read as a CVE, this is a routine kernel-LPE bulletin that aged into a footnote and then reappeared in a federal catalog. The headline action is to confirm the December 2018 update is applied on every still-supported Windows host and move on.
The pattern underneath
The patch is not the story. The fleet is. The reason CVE-2018-8639 is operationally relevant in 2026 is that the population of Windows endpoints which never received the December 2018 cumulative, or which received it and then aged past their support cliff, is still very much in production. The seven-year gap between Microsoft’s fix and CISA’s catalog entry is a measurement of how long it takes for a patched bug to remain useful to attackers, and that measurement is set by lifecycle policy, not by vulnerability research.
Three lifecycle cliffs do most of the work here. Windows 7 ended extended support on January 14, 2020. Commercial Extended Security Updates ran through January 10, 2023, and only customers who paid for all three ESU years are covered through that window. Windows Server 2008 R2 hit the same 2020 cliff, with Azure-hosted ESUs expiring January 9, 2024. Windows Embedded POSReady 7, the retail-and-kiosk variant in ATMs, point-of-sale terminals, and restaurant equipment, shipped its final security updates on October 8, 2024. Anything in that population deployed without the December 2018 cumulative has no vendor-supplied remedy. The CVE is six and a half years old; the exposed device is on a counter taking credit cards.
The industrial tier is where the gap gets uncomfortable. Windows 10 Enterprise 2016 LTSB, version 1607, was the version medical-device vendors, HMI builders, and factory-floor integrators chose precisely because Microsoft promised a decade of stability. It reached security end-of-life in October 2025. TXOne Networks’ 2025 surveys put concrete numbers on the exposure: 44.6 percent of OT organizations run environments where more than half of all endpoints are legacy Windows, and 85 percent say legacy systems limit their ability to apply patches on time. A separate TXOne survey of 550 European OT/ICS decision-makers found that 50 percent confirmed at least half of their OT environments still rely on legacy systems, with 20 percent reporting more than 75 percent legacy dependency. CISA itself flagged Windows 7 and Server 2008 R2 EoL as a critical-infrastructure risk in advisory AA19-290A back in 2019. None of that has been resolved; some of it has just aged out of the news cycle.
The evidence the catalog cares about
CISA’s March 2025 entry sets knownRansomwareCampaignUse: Known. The flag is binary and does not name an operator. The Ransomware Vulnerability Warning Pilot is the documented methodology behind it, but the agency does not publish the per-entry evidence. The most specific public tie to a ransomware-adjacent campaign comes from AhnLab’s February 2023 ASEC report on Dalbit, a Chinese-nexus group also tracked as m00nlight. AhnLab attributed more than 50 confirmed intrusions against South Korean small-to-mid-sized businesses from 2022 onward, with roughly 30 percent sharing a common Korean groupware product. Dalbit’s chain reached for CVE-2018-8639 alongside CVE-2019-1458 and the Potato exploit family to escalate from web-shell-on-internet-facing-server to SYSTEM. Whether Dalbit was the trigger for the 2025 KEV addition, or whether CISA acted on separate classified telemetry, is not in the public record.
A few other pieces of evidence sit next to the catalog entry. Microsoft Defender has carried the signature Exploit:Win64/CVE-2018-8639!MTB since June 11, 2019. Public PoC code has been on GitHub since 2018–2019. The bug fits the well-documented Win32k user-mode-callback pattern Tarjei Mandt described at Black Hat 2011, and which Palo Alto Unit 42 traced through cousins like CVE-2021-1732 and CVE-2022-21882: trigger a callback during teardown, free the target object from user mode, refill the slot, return to the kernel, overwrite a SYSTEM token. The specific vulnerable Win32k function in CVE-2018-8639 is not named in Microsoft’s advisory and no Project Zero or ZDI root-cause writeup specific to this CVE has surfaced, so the primitive is inferred from the bug class rather than confirmed.
What the catalog actually shows is that CVE-2018-8639 is not alone. Per Cyble’s analysis, 94 pre-2024 CVEs were added to KEV in 2025, a 34 percent increase over 2023–2024 norms, with the oldest stretching back to 2007. The interesting question is not “why this one.” It is “why the wave.”
What the pattern means for prioritization
The catalog entry is a signal about where the risk concentrates inside a Windows footprint, not a uniform alert across it. Three tiers fall out of the lifecycle map, and they carry very different weight in a prioritization queue.
In-support, current-patch Windows hosts are at the bottom of that queue. The December 2018 cumulative and every monthly rollup since carries the fix; the kernel-LPE primitive simply is not present on these systems. For this tier, the KEV entry is informational.
Windows 7, Server 2008 R2, and POSReady 7 endpoints without active ESU coverage are where the prioritization weight actually sits. The catalog is naming the kernel-LPE foothold these systems already have. There is no vendor-supplied remedy path for them, so the risk does not retire on a patch calendar; it retires on a decommissioning calendar. That makes them the tier worth knowing by name rather than by class.
Windows 10 1607 LTSB endpoints on medical, industrial, and factory equipment are the slow-moving version of the same exposure. Security end-of-life was October 2025. The CVE-level deadline was March 24, 2025; the fleet-level horizon is 2027 at the earliest, because replacement runs on budget cycles rather than patch windows. In a queue, this tier sits between the other two: not as immediately exposed as the lapsed-ESU population, not as resolved as the in-support one.
The prioritization signal in the KEV addition is not “patch this CVE.” It is the relative weight those three tiers should carry against each other, and the recognition that for two of the three, the work the catalog is pointing at is not patching at all.
What to watch
A 2026 IR report that names CVE-2018-8639 in a current ransomware playbook is the leading indicator. If that surfaces, the March 2025 catalog entry becomes a forward signal rather than a backfill. If it does not, the entry stays in the “catalog catch-up against pre-existing telemetry” bucket, which is its own kind of operational signal: the catalog is being used to surface fleet exposure that everyone already knew about and nobody had owned. GreyNoise and Dark Reading have separately reported that CISA flips the ransomware flag silently via JSON updates without companion advisories, so the absence of an accompanying statement is not unusual; it also is not informative.
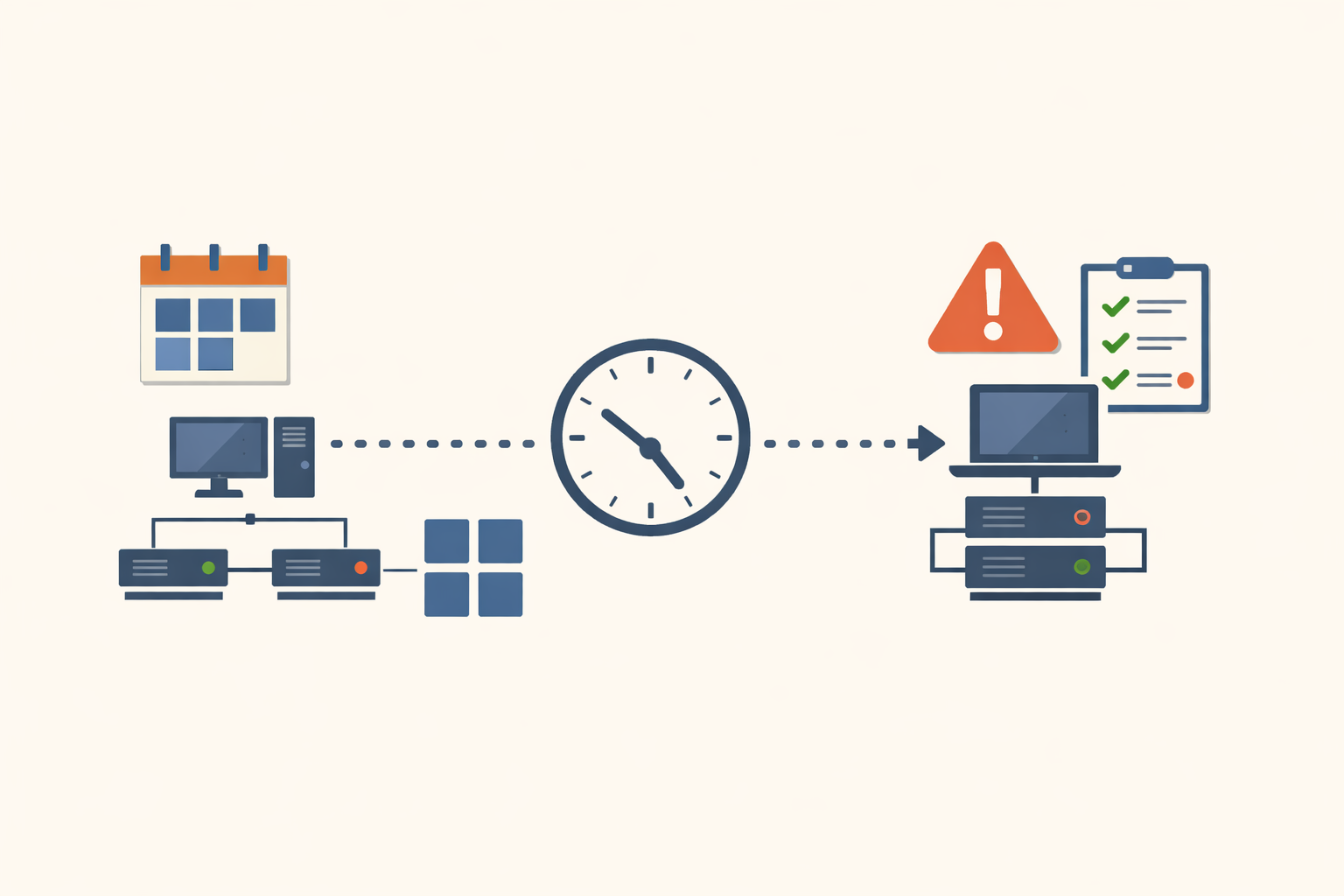
PatchDay Alert flags the CVE-level item the day it lands. The fleet-level question, which Windows lineages a team has quietly decided to keep running past their support cliff, is the one worth a recurring calendar entry of its own.
The number worth tracking is not the age of the next pre-2024 KEV addition. It is the share of an organization’s Windows footprint that sits on a version Microsoft no longer ships fixes for. CVE-2018-8639 is the example. The pattern will produce another one next quarter.
Share
Related field notes
-
The CVSS 4.3 that APT28 was already using
Microsoft shipped the fix for CVE-2026-32202 without an exploitation flag while Russian state actors had a five-month head start. Vendor-tag triage missed it. The federal deadline is tomorrow.
-
The June 2026 Secure Boot cliff: tomorrow is your last clean window
Three Microsoft Secure Boot certificates from 2011 expire in June. May 12 is the last Patch Tuesday before the cliff, and the registry trigger isn't going to set itself.
-
CISA says patch by Friday. Palo Alto's fix ships next Tuesday.
CVE-2026-0300 is an unauthenticated RCE in PAN-OS Captive Portal, exploited since April 9 by a state-aligned actor. The KEV deadline is May 9. The first patch lands May 13. Here's what to do with the four days in between.
One email, every weekday morning.
You're in. Check your inbox.