CISA says patch by Friday. Palo Alto's fix ships next Tuesday.
CVE-2026-0300 is an unauthenticated RCE in PAN-OS Captive Portal, exploited since April 9 by a state-aligned actor. The KEV deadline is May 9. The first patch lands May 13. Here's what to do with the four days in between.
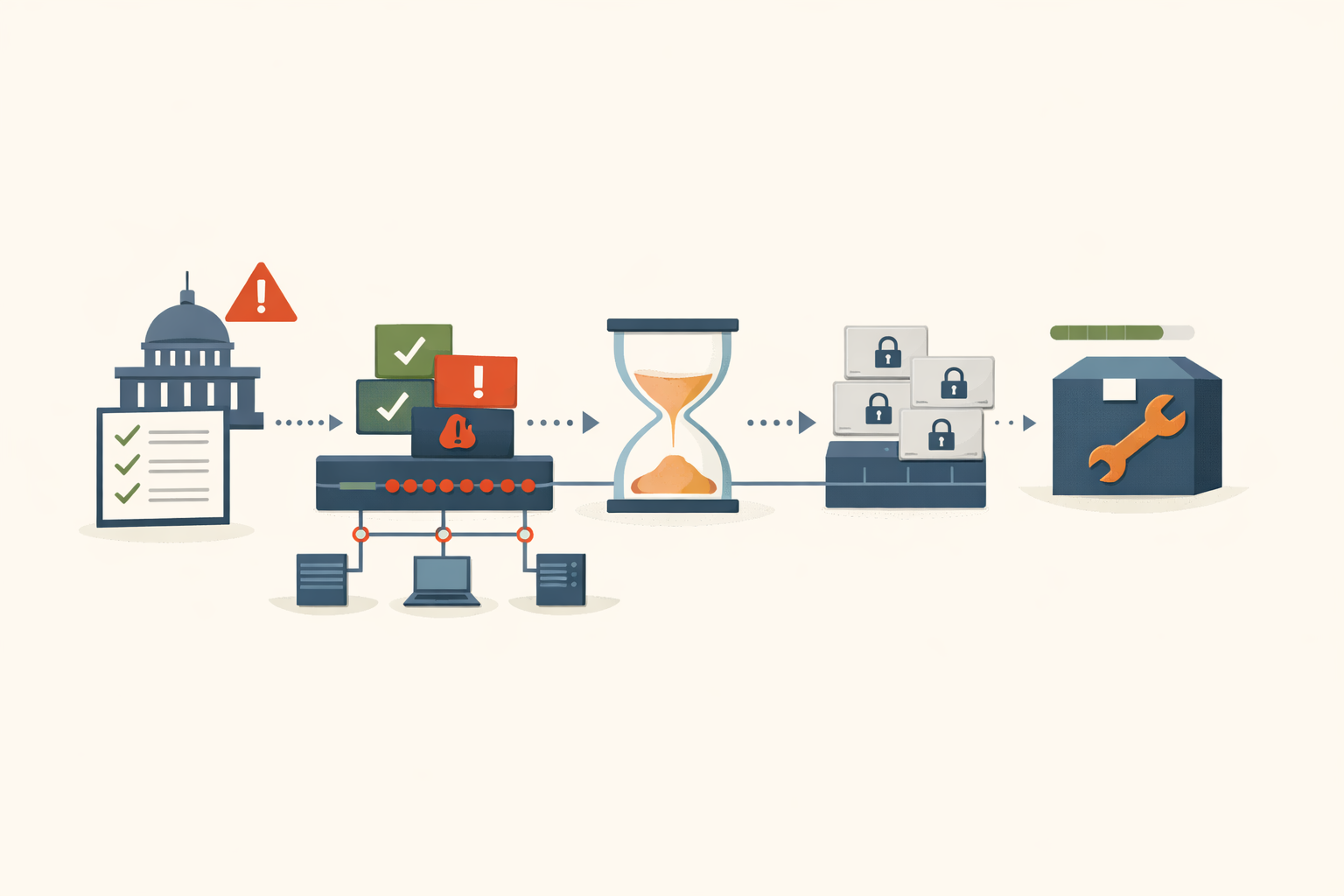
CISA’s remediation deadline for CVE-2026-0300 is May 9. Palo Alto Networks’ first patches ship May 13. That’s a four-day gap between the federal mandate and the vendor’s earliest fix. If you’re a federal agency bound by BOD 22-01, you have been told to remediate a vulnerability for which no patch exists. If you’re a private-sector shop with a change board that meets biweekly, you have a different problem: the mitigation is an emergency change, and the actual upgrade is a second change behind it.
What the vulnerability is
CVE-2026-0300 is an unauthenticated remote code execution in the User-ID Authentication Portal (Captive Portal) on Palo Alto Networks PA-Series and VM-Series firewalls. CVSS 4.0 scores it 9.3; CVSS 3.1 scores it 9.8. The root cause is an out-of-bounds write (CWE-787): the portal fails to validate input length before writing to a fixed-size buffer, and an oversized HTTP POST parameter overwrites adjacent memory. No credentials required. No user interaction. The advisory marks it “automatable,” meaning mass-exploitation tooling can reach it without human intervention.
Two conditions must both be true for exposure: the Captive Portal is enabled (Device > User Identification > Authentication Portal Settings), and Response Pages are enabled on an external-facing interface management profile. Cloud NGFW, Prisma Access, and Panorama are not affected.
Shadowserver tracked over 5,800 globally reachable VM-Series instances as of the advisory date, with heavy concentrations in Asia (2,466) and North America (1,998). PA-Series hardware exposure is not separately quantified.
Who is already inside
A state-aligned threat actor tracked as CL-STA-1132 has been exploiting this since at least April 9, nearly a month before CISA’s KEV listing. Unit 42’s threat brief describes a deliberate, multi-stage campaign. Initial attempts against an internet-exposed portal failed on April 9. The attacker returned and achieved RCE on April 16 by injecting shellcode into an nginx worker process running as root. By April 20, they had deployed tunneling tools (EarthWorm and ReverseSocks5) with root access. On April 29, a SAML flood attack forced a failover that exposed a second device.
The post-exploitation tradecraft is methodical. The attacker cleared crash kernel messages, deleted nginx crash entries and core dump files, wiped ptrace injection evidence from audit logs, and removed SUID binaries. They ran Active Directory enumeration using the compromised firewall’s own service account credentials. This is not someone testing a proof of concept. This is someone who already has a playbook for pivoting from a compromised perimeter device into a domain.
Unit 42 notes that EarthWorm has previously appeared in campaigns linked to Volt Typhoon and APT41, both Chinese-speaking threat groups. Attribution to a specific nation-state is described as “likely” but not confirmed.
No public proof-of-concept code has been released as of May 7. That will change once the May 13 patches enable binary diffing.
Why the patch timeline matters more than the CVSS score
Palo Alto published the advisory on May 5 without patches. Fixed versions arrive in two waves: the first on May 13, the second on May 28, spanning PAN-OS 10.2, 11.1, 11.2, and 12.1. No emergency out-of-cycle hotfixes have been announced.
Compare that to November 2024, when CVE-2024-0012 and CVE-2024-9474 (Operation Lunar Peek, also PAN-OS) shipped patches on the same day as the advisory. This time, the advisory arrived eight days before the first fix. For a vulnerability with confirmed nation-state exploitation and root-level access, that’s a significant change in response posture.
CISA’s 3-day deadline also deserves context. BOD 22-01 typically gives FCEB agencies 14 days for critical KEV additions. Reuters reported on May 1 that CISA is considering a new policy cutting KEV deadlines to 72 hours for critical flaws, citing AI-assisted exploitation speed. Whether CVE-2026-0300 is a formal test of that posture or a severity-driven one-off is unconfirmed. Either way, the practical effect is the same: a deadline that precedes the fix.
What to do before May 13
The realistic interpretation of the May 9 deadline is “implement network-restriction mitigation,” not “install a fix that doesn’t exist yet.” Here’s the triage path.
Check exposure. Device > User Identification > Authentication Portal Settings for Captive Portal status. Network > Interface > [Interface] > Advanced Tab for any Interface Management Profile with Response Pages enabled on internet-facing interfaces. If both conditions are true, the device is in the window.
Restrict portal access to trusted internal zones. This is the recommended mitigation and the one most environments can execute without breaking critical functionality. It eliminates internet-facing exposure while keeping the portal available for internal flows. Per the advisory, this drops the CVSS from 9.3 to 8.7. For most environments, that’s low-risk enough to justify an emergency change outside the normal CAB cycle.
Disable Response Pages on external-facing interface management profiles. This removes one of the two conditions required for exposure without touching the portal itself.
If Captive Portal is not operationally required, disable it entirely. Cleanest option. But it breaks guest WiFi authentication, BYOD onboarding, and any network access control policy that depends on user identity mapping before granting zone access. Know what depends on it before you flip the switch.
Enable Threat Prevention Signature ID 510019 (content version 9097-10022+, PAN-OS 11.1+ only). Treat this as a detection aid, not a substitute for patching. And it only covers the 11.1+ train, leaving PAN-OS 10.2 without a detection-layer option.
Detection is thin. No public IOCs or packet-level signatures as of May 7. In the absence of published signatures, watch for anomalous outbound connections from the management plane and downstream indicators consistent with CL-STA-1132 tradecraft: EarthWorm tunneling, AD enumeration from the firewall’s service account, and evidence of cleared logs (crash kernel messages, nginx crash entries, core dumps).
Planning the actual upgrade
Once the May 13 patches ship, the upgrade itself flows through normal change management. Affected versions span PAN-OS 10.2 (through 10.2.18-h6), 11.1 (prior to 11.1.15), 11.2 (prior to 11.2.12), and 12.1 (prior to 12.1.7). The second patch wave on May 28 covers remaining branches.
VM-Series deployments have an advantage here: snapshot-and-restore workflows can compress the upgrade window significantly compared to physical PA-Series hardware that requires a formal maintenance window.
For private-sector shops with standard 1-2 week CAB cycles, the network restriction is an emergency change this week. The OS upgrade is a scheduled change once the patch train arrives. Two changes, two tickets, two approvals. Budget accordingly.
The window
Not everything with a 9.8 CVSS is operationally urgent. This one is. The attacker is already inside networks, has a repeatable playbook, and the only barrier to broader exploitation is a patch release that enables reverse engineering.
Restrict the portal this week. Schedule the upgrade for the week of May 13. PatchDay Alert’s daily digest covers the operational timeline for vulnerabilities like this, so you’re not reconstructing it from three different vendor pages on a Wednesday morning.
The mitigation is straightforward. The bureaucratic friction of fitting two changes into one week’s change process is the real constraint for most shops. Start that conversation today.
Sources
- CVE-2026-0300 PAN-OS Security Advisory
- Unit 42 Threat Brief: Exploitation of PAN-OS Captive Portal Zero-Day
- NVD - CVE-2026-0300
- BOD 22-01: Reducing the Significant Risk of Known Exploited Vulnerabilities
- ETR: Critical Buffer Overflow in PAN-OS User-ID Authentication Portal - Rapid7
- Palo Alto Networks warns of actively exploited firewall zero-day - Bleeping Computer
- CVE-2024-0012 PAN-OS Advisory (Operation Lunar Peek)
Share
Related field notes
-
Three root shells in seven months. All from the same firewall.
CVE-2024-3400, CVE-2024-0012, and CVE-2024-9474 gave attackers unauthenticated root on Palo Alto firewalls twice in 2024. The pattern isn't bad luck. It's the architecture.
-
SAP NetWeaver was owned for ten weeks before anyone said anything
Five threat groups were already inside SAP NetWeaver when the emergency patch shipped. One confirmed victim reported multi-billion dollar profit impact. SAP's initial workaround guidance was later marked 'Do Not Use.'
-
Your firewall management console was the breach. Cisco FMC CVE-2026-20131.
CVSS 10.0 unauthenticated RCE in Cisco FMC was exploited as a zero-day for 36 days. Here's what the upgrade actually looks like.
One email, every weekday morning.
You're in. Check your inbox.