Ivanti EPMM has produced a confirmed zero-day every year since 2023. Here's the full chain.
Twelve CVEs. Four exploitation waves. Three years. One product line. A complete accounting of Ivanti EPMM's zero-day history, from the Norwegian government breach to this week's credential chain.
In July 2023, Norway’s cybersecurity agency held a press conference to announce that 12 government ministries had been breached through their mobile device management platform. The product was Ivanti EPMM. The bug was CVE-2023-35078, a CVSS 10.0 unauthenticated API access flaw so straightforward that attackers had been exploiting it since at least April of that year. That should have been the single worst thing to happen to EPMM’s reputation. Instead, it was the first item on a list that is still growing.
Three years later, Ivanti EPMM has produced confirmed-exploited zero-days in 2023, 2025, January 2026, and May 2026. Twelve CVEs across four exploitation waves, each chained with the last, each one lowering the bar for the next. State-sponsored actors from at least two distinct groups. A joint CISA/NCSC-NO advisory, three-day KEV deadlines, and a vendor CEO who promised a “secure-by-design” overhaul that has not yet produced a year without an exploited zero-day. This is the full accounting.
2023: the Norwegian government compromise
Norwegian incident response firm mnemonic discovered CVE-2023-35078 during forensic work on what turned out to be one of the largest government breaches in Scandinavian history. The vulnerability was unauthenticated API access. No credentials needed. An attacker could hit /mifs/aad/api/v2/authorized/users and pull PII for every enrolled user, create admin accounts, or modify server configuration. CVSS 10.0, and the score was honest.
The attack hit the IT platform run by DSS, Norway’s Government Security and Service Organisation, which provides shared services to 12 of 16 government ministries. The Prime Minister’s Office, Ministry of Defense, Ministry of Justice, and Ministry of Foreign Affairs were spared because they run separate systems. The CISA/NCSC-NO joint advisory (AA23-213A, published August 1, 2023) confirmed exploitation dating back to at least April. The attackers routed through compromised SOHO routers, including ASUS devices, as relay infrastructure. No nation-state was publicly named, though the tradecraft was described as APT-grade.
Ivanti patched on July 23. CISA added it to the KEV catalog two days later.
Within a week, a second bug surfaced. CVE-2023-35081 (CVSS 7.2) was a directory traversal that let an authenticated admin write arbitrary files to the server. In isolation, a 7.2 requiring admin auth. In practice, attackers had already used CVE-2023-35078 to create admin accounts, which meant the path traversal was free. The chain gave them webshell deployment on the EPMM appliance. CISA added it to the KEV catalog July 31. The joint advisory confirmed both CVEs were used together in the Norwegian government attack.
Then came CVE-2023-38035 (CVSS 9.8), an authentication bypass in Ivanti Sentry, a separate product that often sits alongside EPMM in the same deployment. Sentry’s admin portal on port 8443 could be reached without authentication due to misconfigured Apache HTTPD rules, giving attackers file read/write and OS command execution as root. CISA added it to the KEV catalog one day after disclosure, the kind of turnaround that signals exploitation was already confirmed before the advisory went public. The Sentry bug was not EPMM proper, but it was explicitly part of the same attack chain: compromise EPMM via 35078/35081, then pivot to Sentry.
One more. CVE-2023-35082 (CVSS 10.0) was discovered by Rapid7 in early August 2023 as a patch bypass for CVE-2023-35078. The original fix only covered supported EPMM versions (11.8+). CVE-2023-35082 extended the same unauthenticated API access vulnerability to the entire MobileIron Core lineage, versions 11.7 and below, which many organizations still ran because MobileIron was only rebranded to EPMM relatively recently. CISA did not add it to the KEV catalog until January 18, 2024, when active exploitation was confirmed against legacy deployments that thought they were out of scope.
Four CVEs in a single summer. Three directly in EPMM, one in Sentry via EPMM as the pivot. A government compromised. A joint international advisory. And this was just the beginning.
2025: China comes calling
Eighteen months of relative quiet ended in May 2025. CVE-2025-4427 and CVE-2025-4428, disclosed May 13 and added to the KEV catalog May 19, were a new bug class but the same outcome.
CVE-2025-4427 (CVSS 5.3) was a Spring Security misconfiguration. Missing <intercept-url> rules left routes like /rs/api/v2/featureusage exposed without authentication. On its own, a medium-severity information leak. CVE-2025-4428 (CVSS 7.2) was the payload: user input in the format parameter passed through Spring’s AbstractMessageSource, which evaluated it as Java Expression Language. That evaluation hit Runtime.exec(). The chain gave unauthenticated attackers arbitrary command execution. watchTowr published a full technical breakdown and PoC within two days of disclosure. They confirmed that bean-validation ran before Spring Security’s authorization checks, which meant the malicious payload was evaluated even though the request should have been blocked.
This time, the threat actor had a name. EclecticIQ attributed exploitation with high confidence to UNC5221, a China-nexus cyber-espionage group previously linked to the Ivanti Connect Secure campaigns of early 2024. The same group, back for a different Ivanti product. Post-exploitation, UNC5221 deployed KrustyLoader, a Rust-based loader that fetches an AES-128-CFB encrypted Sliver C2 backdoor from attacker infrastructure, decrypts it with a hardcoded key, and injects it into memory as shellcode. No file on disk. Persistent remote access through a payload that had already been observed in the January 2024 Connect Secure exploitation attributed to the same group.
Targets spanned healthcare, telecommunications, aviation, municipal government, finance, and defense across Europe, North America, and Asia-Pacific. Shadowserver counted 798 internet-facing vulnerable instances as of late May 2025.
Ivanti said the root cause was in two open-source libraries and did not name them. The bugs were in their product, in their security configuration, exposed on their default management interface. Where the libraries came from is trivia. That the management API was reachable unauthenticated is architecture.
January 2026: the harvest
CVE-2026-1281 and CVE-2026-1340 arrived together on January 29, 2026. Both pre-authentication RCE. Both CVSS 9.8. Both exploited as zero-days before patches shipped.
The exploitation was not subtle. GreyNoise recorded 417 exploitation sessions against CVE-2026-1281 in the first nine days after disclosure. 83% of that traffic came from a single IP address on PROSPERO/Proton66 bulletproof hosting infrastructure. That is not opportunistic scanning. That is a threat actor with dedicated infrastructure who was ready on day one, or before it.
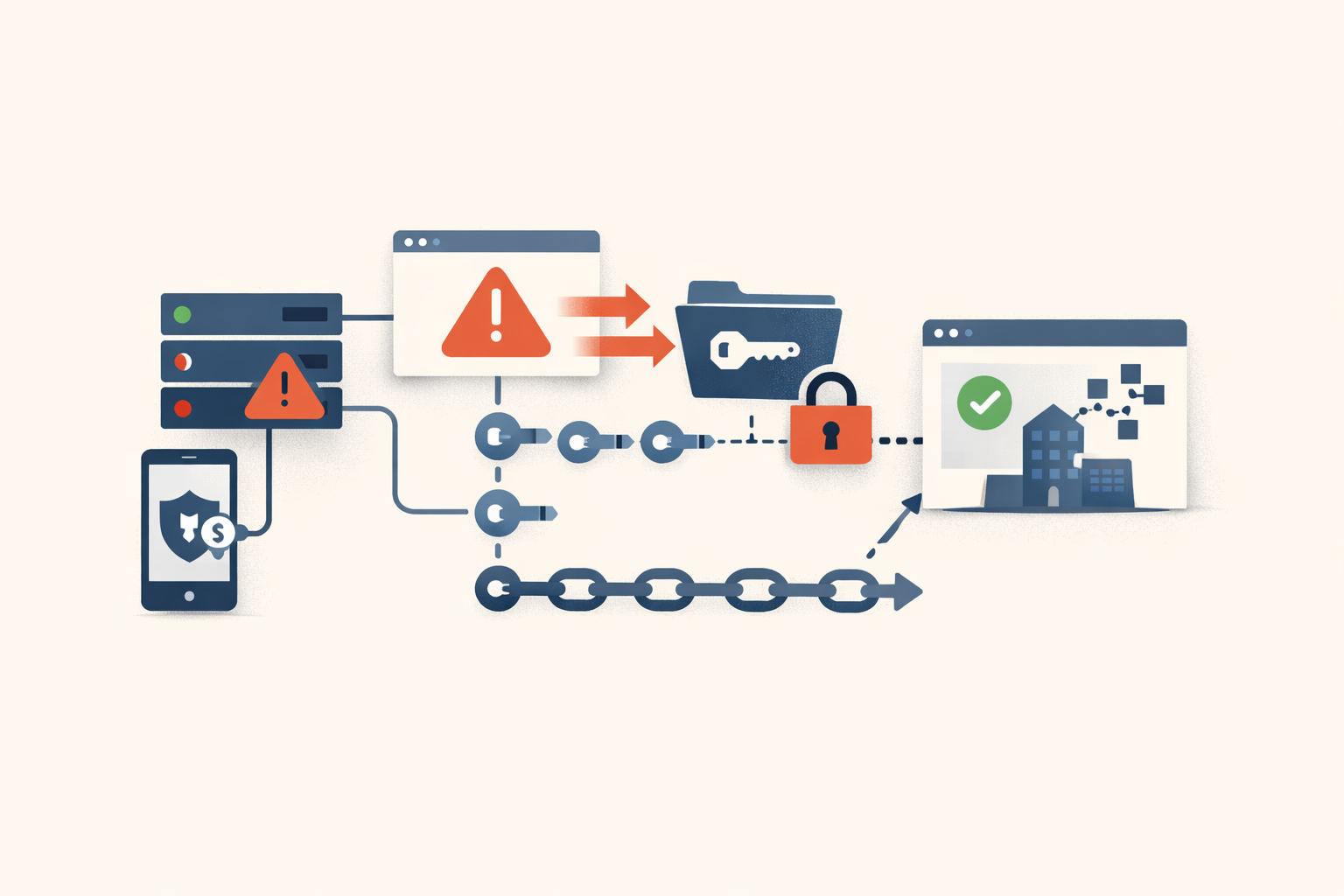
What makes this pair different from earlier waves is what was harvested. The January bugs were pre-auth: no credentials needed to exploit them. But the exploitation itself captured credentials, admin sessions, and configuration data from every EPMM server that was hit. Those credentials did not expire when the patch was applied. They sat in the attacker’s collection, waiting for the next bug that needed them.
Organizations that patched in January but did not rotate every admin credential left the door closed and the key under the mat.
May 2026: the chain completes
On May 7, 2026, Ivanti disclosed CVE-2026-6973, an authenticated RCE in EPMM. CVSS 7.2. Requires admin privileges. Normally that requirement softens the urgency.
Except Ivanti also stated, with “high confidence,” that the admin credentials attackers are using to exploit this bug came from CVE-2026-1340. The one they patched in January. The one many organizations patched without rotating credentials, because the advisory did not explicitly say “your admin passwords are compromised.” For those organizations, the “requires admin authentication” field in the CVSS vector provides no resistance. The authentication barrier was defeated four months ago by the previous vulnerability in the same product.
CISA added CVE-2026-6973 to the KEV catalog same-day with a three-day remediation deadline. May 10. That is among the shortest windows in the catalog’s history, matching the three-day deadline CISA gave CVE-2026-1340 back in April. When CISA compresses a deadline by 79% from the standard 14 days, they are telling you something about exploitation tempo that Ivanti’s “very limited” language does not.
The May advisory bundles five CVEs total. CVE-2026-5787 (CVSS 8.9) enables Sentry impersonation through improper certificate validation. CVE-2026-5786 (CVSS 8.8) is an access control failure. CVE-2026-5788 (7.0) is another access control issue. CVE-2026-7821 (7.4) involves Apple DEP certificate validation. Only CVE-2026-6973 is confirmed exploited. The others have not been observed in the wild yet. “Yet” is doing a lot of work in that sentence given this product’s track record.
The CVE ledger
| Year | CVEs | CVSS | What happened |
|---|---|---|---|
| 2023 | CVE-2023-35078 | 10.0 | Unauthenticated API access. 12 Norwegian government ministries breached. |
| 2023 | CVE-2023-35081 | 7.2 | Directory traversal. Chained with -35078 for webshell deployment. |
| 2023 | CVE-2023-35082 | 10.0 | Patch bypass extending -35078 to legacy MobileIron Core. |
| 2023 | CVE-2023-38035 | 9.8 | Sentry auth bypass. Chained with EPMM compromise as pivot. |
| 2025 | CVE-2025-4427 + CVE-2025-4428 | 5.3 / 7.2 | Auth bypass + EL injection = unauth RCE. UNC5221 deployed KrustyLoader. |
| 2026 Jan | CVE-2026-1281 + CVE-2026-1340 | 9.8 / 9.8 | Pre-auth RCE pair. 417 exploitation sessions in 9 days. Credentials harvested. |
| 2026 May | CVE-2026-6973 | 7.2 | Auth RCE using credentials stolen in January. 3-day CISA deadline. |
Eleven EPMM CVEs plus one Sentry CVE exploited via EPMM as pivot. All confirmed exploited in the wild. All in the CISA KEV catalog. One product line.
Why the architecture is the problem
Every vendor ships bugs. The question is whether the architecture limits the blast radius when a bug lands. EPMM’s architecture does not.
The management API has repeatedly been reachable without authentication. When authentication exists, the credential store has been compromised by prior bugs in the same product. The appliance sits at the network edge, on-premises, managing every enrolled mobile device in the fleet. A compromised EPMM server is not a web application with a narrow blast radius. It is infrastructure that pushes policy, configuration, and certificates to endpoints. It is an MDM takeover.
In April 2024, after the Connect Secure cascade that prompted CISA Emergency Directive ED-24-01, Ivanti CEO Jeff Abbott published an open letter calling the experience “humbling” and promising a secure-by-design overhaul. That letter is now two years old. Since it was published, EPMM alone has produced CVE-2025-4427, CVE-2025-4428, CVE-2026-1281, CVE-2026-1340, and CVE-2026-6973. All exploited in the wild. All in the KEV catalog.
“Secure by design” means the architecture resists exploitation even when individual bugs exist. Defense in depth, privilege separation, minimal attack surface on management interfaces. Three years of evidence suggests EPMM’s architecture does not provide that resistance. The bugs keep arriving pre-auth, the chains keep working, and the credentials from the last incident keep enabling the next one.
The exposure right now
Shadowserver counts roughly 850 internet-exposed EPMM instances as of early May 2026, down from about 1,600 in February. That reduction likely followed the January CVE-2026-1340 disclosure. The remaining 850 had four months to act on a CVSS 9.8 pre-auth RCE and did not.
Ivanti claims over 40,000 customers and 96 of the Fortune 100. Government and regulated industries are the heaviest on-prem EPMM adopters due to data-residency requirements. NIH is a named reference customer. If you are running EPMM on-premises, you are running a product that has been targeted by unnamed APT actors, UNC5221 (China-nexus), and at least one operator with dedicated bulletproof hosting infrastructure, across four separate exploitation campaigns, in three years.
What you should actually do
If you are still running EPMM, patch to 12.6.1.1, 12.7.0.1, or 12.8.0.1 for the May 2026 advisory. Ivanti says the upgrade takes seconds with no downtime. Then rotate every admin credential on the appliance. Not just the ones you think were compromised. All of them. The January pair drew 417 exploitation sessions in nine days; you do not know which credentials were harvested unless you have continuous session logging that you have actually reviewed.
Check /var/log/httpd/https-access_log for anomalous requests to admin endpoints. Restrict the admin interface (port 8443) to internal networks only. Treat the EPMM appliance the way you would treat a domain controller: isolated, monitored, with no assumption that the network around it is clean.
And start the harder conversation. EPMM has produced a confirmed-exploited zero-day in every year since 2023. Each vulnerability created the preconditions for the next. The credential chain from January to May 2026 is not a coincidence; it is a pattern completing. At some point, the question stops being “did you patch the latest one?” and becomes “why is this product still in your architecture?”
PatchDay Alert has flagged every EPMM KEV entry as it landed: CVE-2026-1340 in April, CVE-2026-6973 in this week’s digest, and the chain between them is exactly the kind of cross-CVE context that single-vulnerability advisories miss. The next EPMM zero-day is not a question of if. The only question is whether the credentials from this round will still be valid when it arrives.
Sources
- Ivanti Security Advisory: EPMM (May 2026)
- CISA Known Exploited Vulnerabilities Catalog
- CISA/NCSC-NO Joint Advisory AA23-213A: Ivanti EPMM
- CISA Emergency Directive ED-24-01: Ivanti Connect Secure
- NVD: CVE-2023-35078
- NVD: CVE-2023-35081
- NVD: CVE-2023-35082
- NVD: CVE-2025-4427
- NVD: CVE-2025-4428
- NVD: CVE-2026-1281
- NVD: CVE-2026-1340
- NVD: CVE-2026-6973
- mnemonic: Ivanti EPMM Authentication Bypass (CVE-2023-35078)
- EclecticIQ: China-Nexus Threat Actor Exploiting CVE-2025-4428
- watchTowr: Expression Payloads Meet Mayhem (CVE-2025-4427, CVE-2025-4428)
- GreyNoise: Active Ivanti Exploitation Traced to Single Bulletproof IP
- Unit 42: Critical Vulnerabilities in Ivanti EPMM
- CCB Belgium: Authenticated RCE in Ivanti EPMM Exploited
- BleepingComputer: Ivanti warns of new EPMM flaw exploited in zero-day attacks
- BleepingComputer: CISA confirms CVE-2023-35082 actively exploited
- The Register: Ivanti commits to secure-by-design overhaul
Share
Related field notes
-
Ivanti Connect Secure: the perimeter that keeps breaking
Five KEV-listed Ivanti Connect Secure bugs in fifteen months, all ransomware-tagged, all on the unauthenticated path. The pledge bought goodwill. The code did not change.
-
Three root shells in seven months. All from the same firewall.
CVE-2024-3400, CVE-2024-0012, and CVE-2024-9474 gave attackers unauthenticated root on Palo Alto firewalls twice in 2024. The pattern isn't bad luck. It's the architecture.
-
CISA says patch by Friday. Palo Alto's fix ships next Tuesday.
CVE-2026-0300 is an unauthenticated RCE in PAN-OS Captive Portal, exploited since April 9 by a state-aligned actor. The KEV deadline is May 9. The first patch lands May 13. Here's what to do with the four days in between.
One email, every weekday morning.
You're in. Check your inbox.