SmarterMail's ConnectToHub API gave attackers SYSTEM in a single POST request
CVE-2026-24423 is an unauthenticated RCE in SmarterMail's ConnectToHub API. No credentials, no interaction, CVSS 9.8, confirmed ransomware. One of three critical SmarterMail CVEs in ten days. Here's what happened and what to do about it.
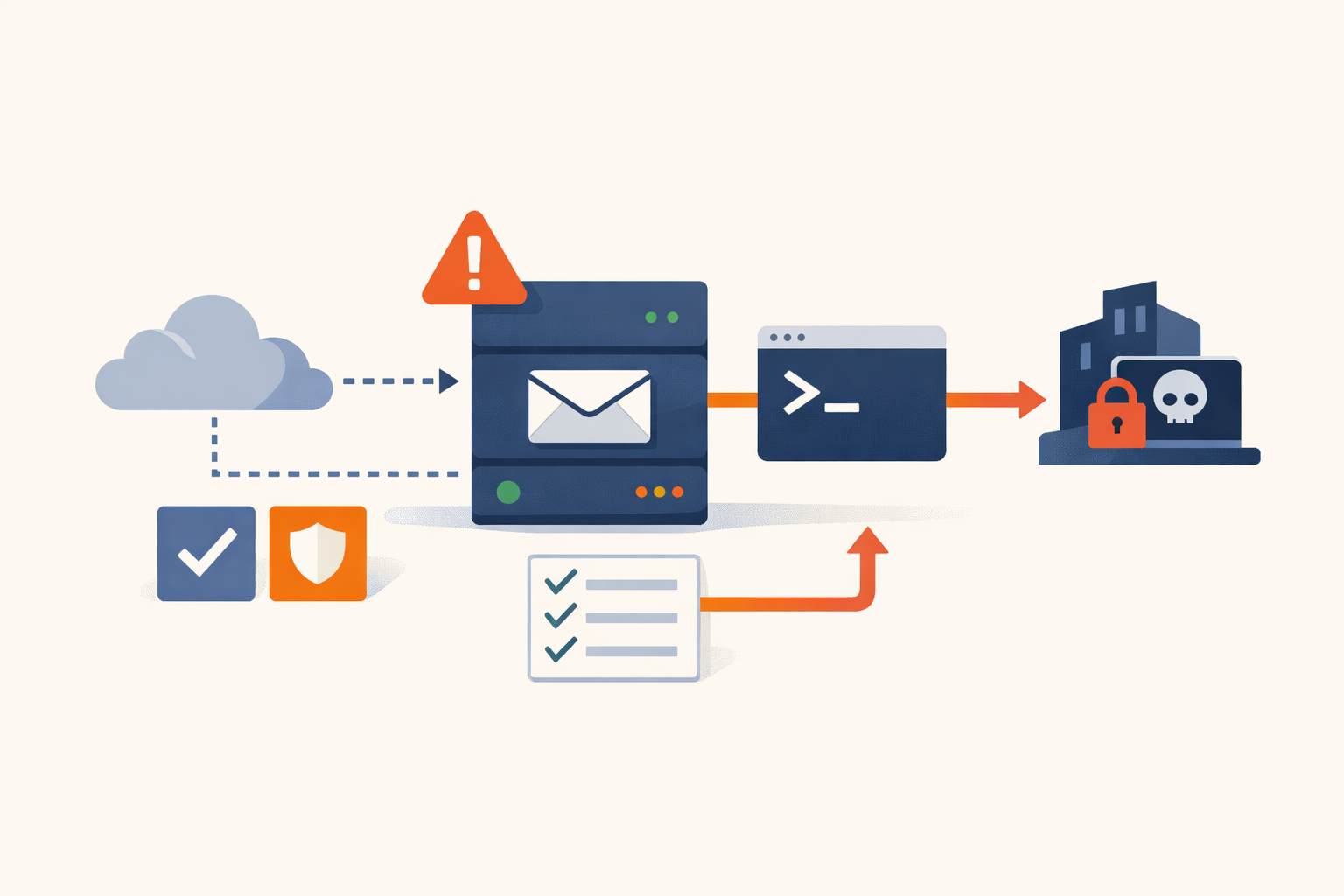
SmarterMail has a feature called ConnectToHub that links an installation to a SmarterTools management server. The API endpoint for it, /api/v1/settings/sysadmin/connect-to-hub, requires no authentication. Send it a POST with a URL you control, and SmarterMail calls your server, downloads a JSON payload, and passes the commands inside it directly to the operating system shell. CVSS 9.8. No credentials, no user interaction, full SYSTEM-level code execution on Windows.
That’s CVE-2026-24423, and it was one of three critical SmarterMail vulnerabilities added to the CISA KEV catalog in a ten-day window. Storm-2603 used it to deploy Warlock ransomware. The targets included SmarterTools itself.
How ConnectToHub becomes an RCE
The ConnectToHub feature is meant for managed hosting setups where SmarterMail nodes register with a central hub. The endpoint accepts a hubAddress parameter and makes an outbound HTTP GET to {hubAddress}/web/api/node-management/setup-initial-connection. The response includes a CommandMount field. SmarterMail takes that value and passes it directly to cmd.exe on Windows or /bin/bash on Linux.
Three weaknesses compound: the endpoint is decorated with AllowAnonymous = true, bypassing all authentication middleware. The server fetches an attacker-supplied URL without validation. And the JSON it receives is deserialized straight into a shell call with no sanitization. The whole attack is one POST request followed by an outbound callback. VulnCheck, Code White, and watchTowr all independently found the flaw. Build 9511, released January 15, 2026, removed unauthenticated access to the endpoint.
Who runs SmarterMail and why that matters
SmarterMail is a Windows-based mail server positioned as a lower-cost Exchange alternative. SmarterTools’ primary audience is web hosting providers and ISPs who resell mailboxes to SMB clients. The company claims 15 million users across 120 countries. Named customers are mostly hosting-stack companies, which means the end-user count is heavily decoupled from the install count. Each hosting provider serves hundreds or thousands of downstream tenants.
The product runs on Windows Server with IIS and must be internet-facing on SMTP, IMAP, POP3, and HTTPS to function as a mail server. The sysadmin API rides on the same HTTPS port as webmail. There is no split between the management plane and the mail plane. Shadowserver identified over 6,000 internet-exposed SmarterMail servers likely vulnerable at disclosure. A separate researcher count placed the number at 8,001 unique IPs, concentrated in the US (4,100+), Malaysia, India, Canada, and the UK.
When an attacker compromises a hosting provider’s SmarterMail instance, the blast radius extends to every mailbox on that server: email content, attachments, calendars, contacts, and admin credentials for all hosted domains. For MSP deployments, that can mean lateral movement into downstream customer environments.
Three CVEs in ten days
CVE-2026-24423 was not an isolated incident. CISA added three SmarterMail vulnerabilities to the KEV catalog between January 26 and February 5, 2026. They are parallel paths to the same outcome, not a single chain.
CVE-2025-52691 (CVSS 10.0) was an unrestricted file upload via /api/upload. Path traversal through the guid parameter let an attacker write a .aspx web shell directly into the IIS webroot. Patched silently in Build 9413 on October 9, 2025, with no CVE assigned and no public advisory. watchTowr’s December 2025 analysis revealed the vulnerability had been quietly fixed for two months, raising questions about whether it was exploited during the gap. Censys observed approximately 16,000 exposed instances.
CVE-2026-23760 (CVSS 9.3) was an authentication bypass via the force-reset-password API endpoint. An unauthenticated POST with IsSysAdmin: true forced a system administrator password reset without verification. From there, the built-in Volume Mount feature could be abused for command execution. Exploitation in the wild was observed within two days of the patch being reverse-engineered. ReliaQuest attributed this as Storm-2603’s primary initial access vector in the Warlock ransomware campaign.
All three are addressed by Build 9511 or later. CVE-2025-52691 was actually patched in the earlier Build 9413, but Build 9511 subsumes that fix alongside the two January 2026 patches. The pattern across them is consistent: unauthenticated access to administrative API endpoints that should never have been exposed. SmarterMail’s security track record stretches back to at least 2019, when NCC Group disclosed CVE-2019-7214 (CVSS 9.8), an insecure .NET deserialization that gave SYSTEM-level RCE. Pre-auth access to privileged endpoints is a structural pattern in this product, not isolated incidents.
The SmarterTools breach
On January 29, 2026, Storm-2603 (also tracked as Gold Salem) breached SmarterTools’ own infrastructure. An employee-managed virtual machine on the office network had not been updated to Build 9511, which had been released two weeks earlier.
The post-exploitation chain, documented by ReliaQuest and The Hacker News: attackers downloaded a malicious MSI installer from Supabase infrastructure, installed Velociraptor as their C2 tool, and detonated Warlock ransomware approximately one week later. Roughly 12 Windows servers on the office network and a secondary QC data center were encrypted. SmarterTools stated that customer-facing services were unaffected.
The irony is the obvious part. The more operationally relevant detail: Storm-2603 consistently waited 6-7 days between initial access and ransomware deployment. Organizations that patched after the exploitation window opened but before the ransomware fired may have closed the front door while the attacker was already inside. Post-patch, the question isn’t just “did I patch?” but “did I patch before they got in?”
What you need to do
Check your version. GET /api/v1/licensing/about returns version info without authentication. Anything below Build 9511 is vulnerable to all three CVEs. Current release is Build 9610. Target the current release, not just the floor.
The update is manual. SmarterMail has no auto-update mechanism. The process: stop the SmarterMail service, back up the installation folder and domain data, download the new installer, uninstall the current version, reinstall to the same path. Configuration and mail data are preserved. Plan for a maintenance window; mail delivery stops while the service is down.
If you can’t patch immediately: Block external access to /api/v1/settings/sysadmin/ API paths at your WAF or reverse proxy. Implement egress filtering so the mail server can’t make outbound HTTP connections to arbitrary destinations. The exploit requires SmarterMail to call the attacker’s server, so blocking outbound traffic to non-whitelisted hosts breaks the attack chain. Neither of these is a substitute for patching, but they buy time.
Check for compromise indicators. Look for any POST requests to /api/v1/settings/sysadmin/connect-to-hub in your logs. On patched systems this returns HTTP 400; on vulnerable systems it executed. Check for unexpected cmd.exe or powershell.exe processes spawned as children of the SmarterMail service. Look for the file C:\Program Files (x86)\SmarterTools\SmarterMail\Service\wwwroot\result.txt, a known reconnaissance artifact from the companion attack chain.
The window
The patch has been available since January 15. CISA’s remediation deadline was February 26. It is now May. The vulnerability has a public technical breakdown from VulnCheck and confirmed ransomware exploitation by Storm-2603. Every unpatched SmarterMail instance that is internet-facing is an open door.
If you’re a hosting provider running SmarterMail for your clients, this isn’t just your server at risk. It’s every mailbox, every domain, every downstream tenant on that instance. PatchDay Alert tracks CISA KEV additions and flags the ones that matter for operations. This is one of them.
The remediation is a manual upgrade that takes a maintenance window. If you haven’t scheduled that window yet, stop reading and schedule it.
Sources
- NVD - CVE-2026-24423
- VulnCheck - Street Smarts: SmarterMail ConnectToHub Unauthenticated RCE
- BleepingComputer - CISA warns of SmarterMail RCE flaw used in ransomware attacks
- Help Net Security - Ransomware attackers exploiting critical SmarterMail vulnerability
- Help Net Security - Ransomware group breached SmarterTools via SmarterMail
- F5 Labs - Looking at the SmarterMail API Vulnerability CVE-2026-24423
- ReliaQuest - Storm-2603 Exploits CVE-2026-23760 to Stage Warlock Ransomware
- The Hacker News - Warlock Ransomware Breaches SmarterTools
- Huntress - SmarterMail Account Takeover Leading to RCE
- Shadowserver - 6,000+ vulnerable SmarterMail servers exposed
- SmarterTools - Official Breach and CVE Summary
- watchTowr - SmarterMail Pre-Auth RCE CVE-2025-52691
Share
Related field notes
-
SmarterMail fixed a CVSS 10 and told no one for two months
CVE-2025-52691 is a pre-auth RCE in SmarterMail's file upload API. SmarterTools patched it silently in October 2025 with no CVE, no advisory, and release notes that said 'critical security fixes.' watchTowr found the silent fix two months later. Here's why that matters.
-
48 hours from patch to exploitation: CVE-2026-23760 and the window that doesn't exist anymore
SmarterMail's patch shipped January 15. Attackers decompiled the .NET assemblies, found the fix, built a working exploit, and were inside production systems by January 17. Then they breached SmarterTools itself.
-
SimpleHelp CVE-2024-57727: a seven-day patch and a sixteen-month leak
SimpleHelp shipped a fix in seven days from full disclosure. Then they posted it to a forum. Ransomware affiliates have been pulling hashed admin credentials out of unpatched servers ever since.
One email, every weekday morning.
You're in. Check your inbox.