Cleo shipped a fix in October. Cl0p was bypassing it by December.
CVE-2024-50623 was patched in 5.8.0.21 on October 27. By December 3, Huntress had a working PoC against fully patched hosts and Cl0p was running it in production. This is the fifth MFT vendor in five years to hand Cl0p the same playbook.
On October 27, 2024, Cleo published CVE-2024-50623 and shipped Harmony, VLTrader, and LexiCom 5.8.0.21 to fix it. Customers patched. On December 3, Huntress reproduced a working exploit against fully patched 5.8.0.21 hosts and notified Cleo. By December 8, Cl0p was running the bypass at scale. The first build that actually closed both bug paths, 5.8.0.24, did not ship until December 11 or 12. Cl0p’s leak-site post a week later was unsentimental: “as for CLEO, it was our project (including the previous cleo).”
This is the fifth managed-file-transfer vendor in five years to be mass-exploited by Cl0p on substantially the same playbook. Accellion FTA in 2020, Serv-U in 2021, GoAnywhere and MOVEit in 2023, Cleo in 2024. The bug classes vary. The deployment posture, the vendor response shape, and the post-exploitation pattern do not. Calling Cleo a Cleo problem misreads the record.
The patch that didn’t patch
CVE-2024-50623 is two failures stacked. The /Synchronization endpoint, intended for file sync between clustered Cleo nodes, validated only that an incoming serial number matched a trivial bitshift scramble, not that it corresponded to a real licensed install. Past that gate, the Retrieve and ADD commands handed an unauthenticated caller arbitrary file read and arbitrary file write against caller-specified paths. The file-write half landed in the Autorun directory, where Cleo’s own watcher unpacked attacker-staged ZIPs and executed an embedded base64 PowerShell payload as the service account. CVSS 9.8. watchTowr Labs published a working PoC.
Cleo’s October fix added a validatePath() function intended to block path-traversal-based writes. By early December, Huntress had confirmed validatePath() was bypassable on 5.8.0.21 and that systems with the patch applied were still being exploited in production. CISA designated the bypass CVE-2024-55956 on December 13 and added both CVEs to KEV within the week, with deadlines of January 3 and January 7, 2025.
Researchers disagree narrowly on whether 55956 is a true bypass of 50623’s fix or a distinct command-injection bug in the Autorun feature itself. Huntress, Darktrace, and most aggregators describe a bypass; Rapid7 argues it is a separate CWE-77 issue with its own root cause. The practical bottom line is the one operators care about: 5.8.0.21 was not safe to run, and Cleo did not say so until customers were already on fire.
The deeper problem is the Autorun directory. It is a documented administrative feature, not an oversight. The default install creates C:\Harmony\autorun\, C:\VLTrader\autorun\, C:\LexiCom\autorun\ and watches them for files to execute. Any file-write primitive anywhere in the product is automatically promoted to code execution. Cleo’s interim mitigation between the second incident and the 5.8.0.24 build was, literally, to clear the Autorun Directory field in Configure → Options → Other. The shipping fix was not a patched function; it was an architectural change to a feature that should not have shipped enabled-by-default in the first place.
Cl0p’s MFT record
Five campaigns. Five vendors. The same workflow each time: acquire or discover a near-zero-day in an internet-facing MFT product, mass-exploit before disclosure, drop a lightweight web shell or RAT for exfiltration, leave encryption out of it, go quiet for weeks, then surface victim names on the Tor leak site with a countdown.
| Year | Product | Bug class | CVE | Reported scale |
|---|---|---|---|---|
| 2020–21 | Accellion FTA | SQLi + OS command injection | CVE-2021-27101..27104 | ~100 orgs |
| 2021 | SolarWinds Serv-U | RCE | CVE-2021-35211 | Smaller, Cobalt Strike + FlawedGrace |
| 2023 | Fortra GoAnywhere | Java deserialization | CVE-2023-0669 | ~130 orgs in ~10 days |
| 2023 | Progress MOVEit | SQL injection | CVE-2023-34362 | 2,600+ orgs, 77M+ individuals |
| 2024 | Cleo Harmony/VLTrader/LexiCom | File write to Autorun RCE | CVE-2024-50623, CVE-2024-55956 | 200+ leak-site claims, 50+ confirmed |
Initial reporting in December 2024 credited a crew called Termite, the same name attached to the Blue Yonder breach. Cl0p later claimed the campaign directly to BleepingComputer and SecurityWeek, and the TTPs match prior Cl0p MFT operations. Whether Termite is a Cl0p rebrand, an affiliate, or a collaborating crew is unresolved in public reporting. The operational handprint is Cl0p’s regardless.
The Cleo post-exploitation framework Huntress named Malichus is a three-stage Java RAT: a PowerShell downloader, an AES-encrypted JAR loader keyed per-payload, and a modular nine-class backdoor that parses Cleo’s own conf/Top.xml and hosts/<hostname>.xml to harvest trading-partner directories before chunking the data out in 262,154-byte ZIP segments. The level of product-specific knowledge in stage three is not the work of a crew that woke up to Cleo last week.
Why MFT keeps being the target
The codebases are old. Accellion FTA was a 20-year-old product running on EOL CentOS 6 at the time it was breached. GoAnywhere accumulated FTP, SFTP, FTPS, AS2, OFTP, HTTPS, SCP, and PeSIT support over its lifetime; the bug Cl0p used was a 2015-vintage Java deserialization class in a license servlet. IBM’s 2025 review of the MFT incidents notes that the affected vendors had few or no full-time security engineers on the product team and no proactive bug-bounty programs. Intel 471 counted roughly 136 MFT vulnerabilities in NVD since 2014, with SQL injection and OS command injection dominating the bug classes. None of this is exotic. These are the bugs a baseline secure-development practice catches.
The deployments are exposed by design. MFT exists to move data between organizations, so the data plane has to be internet-reachable. What does not have to be internet-reachable is the admin UI, and yet Cleo, GoAnywhere, and MOVEit all ship the admin interface on the same listener as the data plane. Beaumont counted more than 1,000 GoAnywhere admin consoles publicly exposed during the early 2023 campaign. Censys counted around 1,442 exposed Cleo instances globally in mid-December 2024, with roughly 70 percent still on vulnerable builds when Cl0p was actively running the campaign.
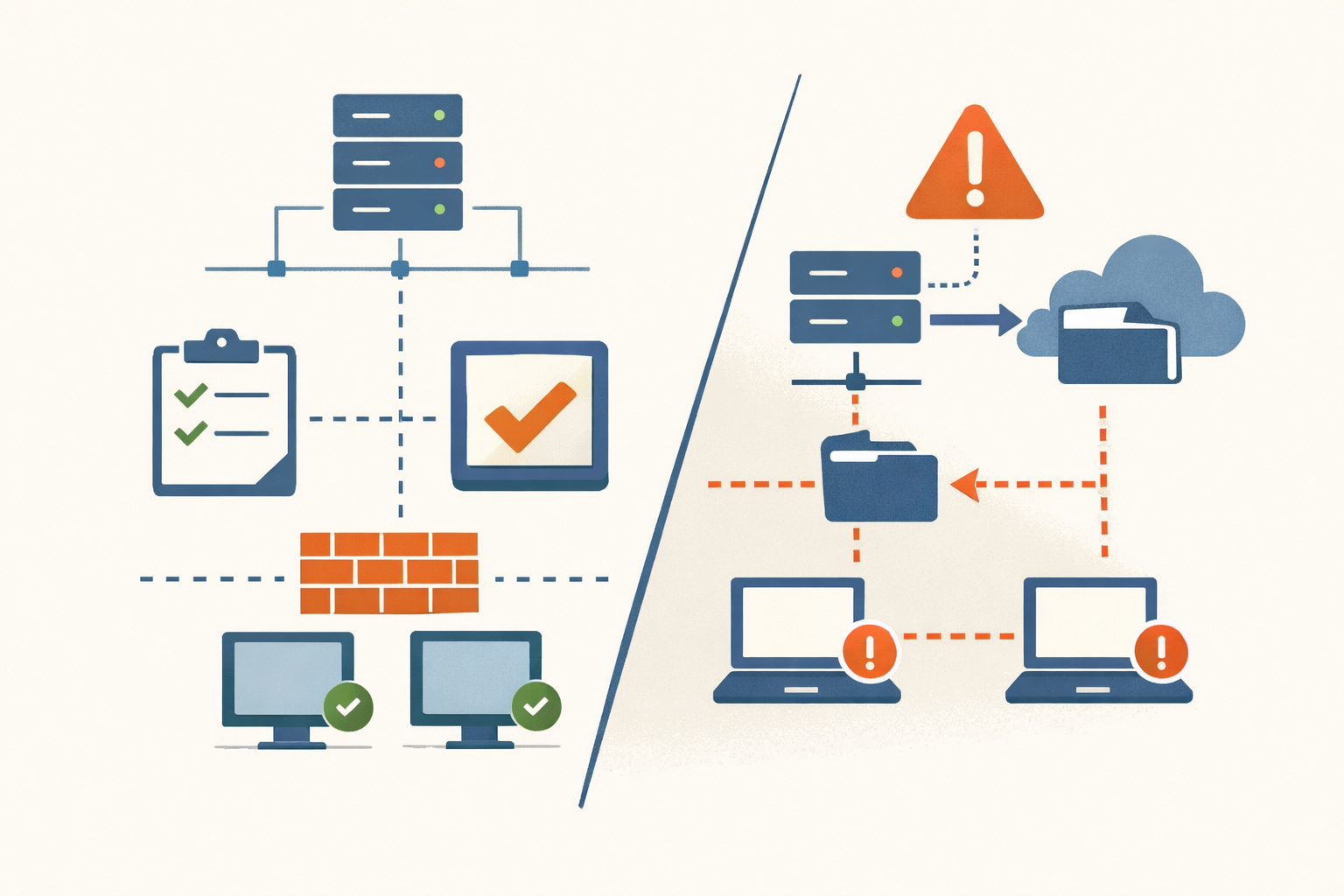
The vendor responses rhyme. Reactive disclosure. Advisories gated behind customer login portals. Fixes that close one path while leaving the architecture intact. Cleo’s October patch is the cleanest recent example of the pattern: a validatePath() function bolted onto a vulnerable codebase, bypassed inside six weeks, with the underlying Autorun feature untouched until a second incident forced the issue.
What to actually do
If you ran Cleo on 5.8.0.21 between roughly December 3, 2024 and the day you applied 5.8.0.24, treat the host as compromised. Preserve <install>\logs\, Windows Event Logs, and EDR telemetry to write-protected storage before patching, before reboot. Look in <install>\autorun\ for healthchecktemplate.txt, healthcheck.txt, and UUID-named XMLs; in <install>\hosts\ for a main.xml containing base64 PowerShell; for cleo.<numeric> JARs outside the program tree; and for the Cleo service spawning java.exe -jar followed by powershell.exe -EncodedCommand. Map the blast radius across every trading partner whose data flowed through the box. Cl0p’s MO is quiet exfiltration, so absence of EDR alerts is not absence of exposure, and the regulatory notification clocks (HIPAA’s 60 days, GDPR’s 72 hours, SEC Item 1.05) start from discovery, not from confirmation.
If you run any other MFT, the lesson is older than this incident. The admin UI does not belong on the internet. The MFT host is Tier 0 in the same sense a domain controller is, because it touches every partner relationship and every data type that flows through your business. Anything that auto-processes a directory, by whatever name the vendor markets it, needs file integrity monitoring and a hard ACL. Patch SLAs for MFT need to be measured in hours, not the standard month, because the threat actor who cares most about your MFT product is on a faster cycle than your change-advisory board.
Five vendors over five years have run the same experiment, and the result is in. Cleo is not the last entry. The next vendor on the list is the one whose admin UI is on the public internet right now, whose security team has not yet been told, and who will read about it in a daily digest like ours the morning a CVE hits KEV.
Sources
- NVD: CVE-2024-50623
- NVD: CVE-2024-55956
- Huntress: Threat advisory — Oh no, Cleo!
- Huntress: Cleo software vulnerability — Malichus malware analysis
- Rapid7: Widespread exploitation of Cleo file transfer software
- watchTowr Labs: Cleo CVE-2024-50623 technical analysis
- Arctic Wolf: Threat campaign targeting Cleo MFT products
- Darktrace: Cleo file transfer vulnerability — patch pitfalls
- BleepingComputer: Clop ransomware claims responsibility for Cleo data theft attacks
- Censys: CVE-2024-55956 advisory
- CISA AA23-158A: CL0P exploits MOVEit CVE-2023-34362
- IBM: Security breaches in Cleo, GoAnywhere and MOVEit (2022–2025)
- Intel 471: Managed file transfer software — assessing the risks
Share
Related field notes
-
SimpleHelp CVE-2024-57727: a seven-day patch and a sixteen-month leak
SimpleHelp shipped a fix in seven days from full disclosure. Then they posted it to a forum. Ransomware affiliates have been pulling hashed admin credentials out of unpatched servers ever since.
-
Three root shells in seven months. All from the same firewall.
CVE-2024-3400, CVE-2024-0012, and CVE-2024-9474 gave attackers unauthenticated root on Palo Alto firewalls twice in 2024. The pattern isn't bad luck. It's the architecture.
-
Ivanti Connect Secure: the perimeter that keeps breaking
Five KEV-listed Ivanti Connect Secure bugs in fifteen months, all ransomware-tagged, all on the unauthenticated path. The pledge bought goodwill. The code did not change.
One email, every weekday morning.
You're in. Check your inbox.